MANAGED SECURITY SERVICES
Identify, Protect, Detect and Recover
HEROIC’s enterprise cybersecurity services help improve overall organizational security with industry best practices and advanced technology solutions.
Enterprise Security Services

Penetration Testing
Penetration testing can help determine whether your systems are vulnerable to attacks and if current defenses are sufficient

Vulnerability Scanning & Assessments
Cybersecurity risk assessments identify the gaps in your organization’s critical risk areas and determine which actions need to be taken to close those gaps.
Data Breach Monitoring & Response
Through easy API access to our DarkHive™ database, we help users quickly protect against login credential misuse and privacy incidents in real-time.

Consulting & Education
We provide an objective view of your corporate cyber posture, consult on improvements, mentor team growth, and provide critical education.
Regulatory Compliance
Our cybersecurity analysts help organizations understand which regulations, policies and requirements need to be met in order to become compliant.

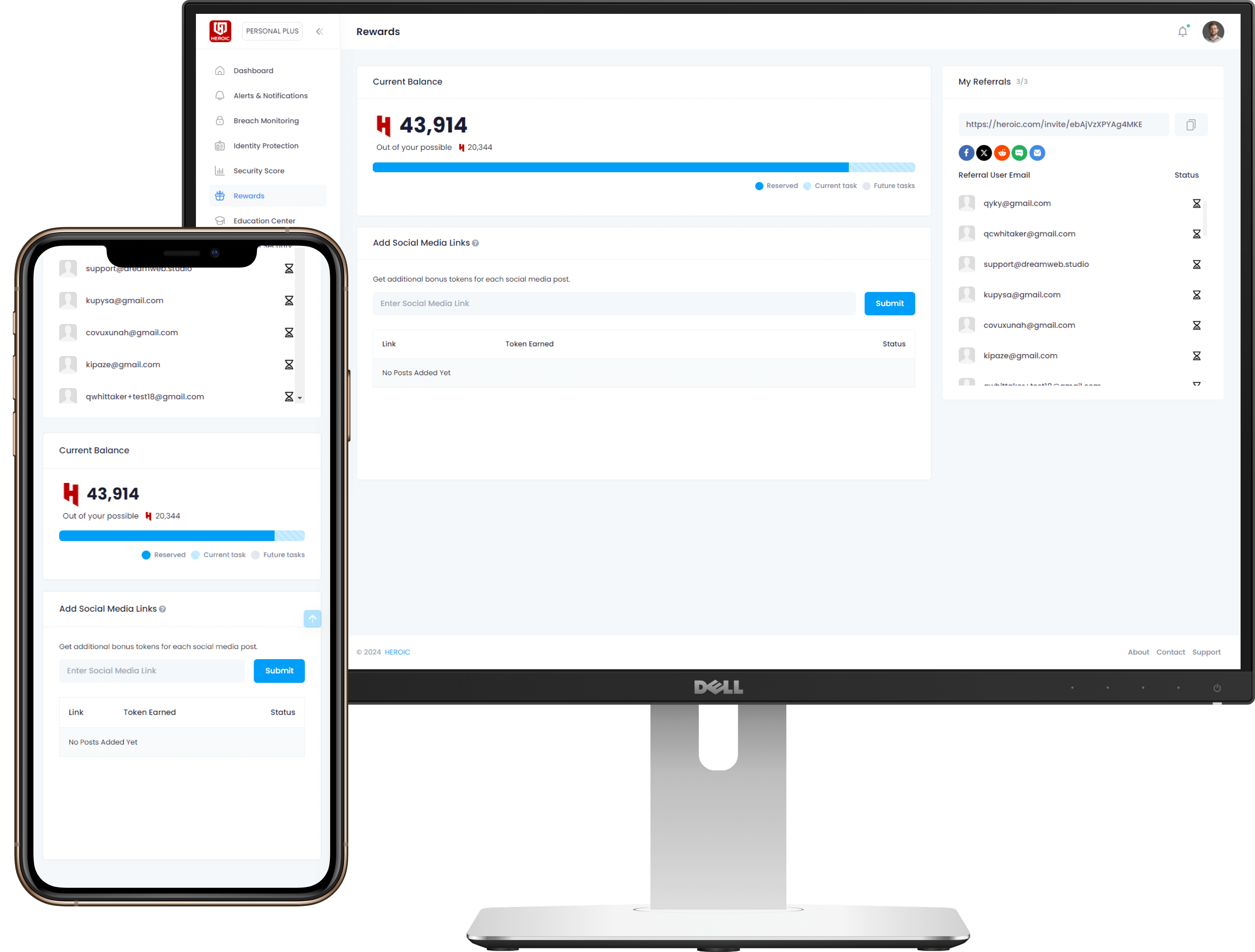
Employee Protection
HEROIC offers organizations with the ability protect employees from data breaches with personal HEROIC accounts and resources to properly protect them.
We Uncover Threats Facing Your Business
Pinpointing weaknesses isn’t always easy. Fortunately, our team of trained security professionals
In order for an organization to keep crucial information – including customer data – and critical systems secure from outsider exploitation, uncovering security threats and vulnerabilities is extremely important.
With that in mind, the HEROIC Enterprise Security Services team can simulate real-world attacks on your networks, applications, devices, and employees to evaluate the strength of your security stance as well as providing detailed reports on how to strengthen it moving forward.
Get in contact with one of our security analysts today!
Get in contact with one of our security analysts now!
We Uncover Threats Facing Your Business
Pinpointing network and endpoint weaknesses aren’t always easy. Fortunately, our team of trained security professionals
Enterprise Security Services
Data Breach Monitoring & Response
Through easy API access to our DarkHive™ database, we help users quickly protect against login credential misuse and privacy incidents in real-time.

Vulnerability Scanning & Assessments
Cybersecurity risk assessments identify the gaps in your organization’s critical risk areas and determine which actions need to be taken to close those gaps.

Consulting, Education & Policy Management
We provide an objective view of your corporate cyber posture, consult on improvements, mentor team growth, and provide critical education.

Individual Services
HEROIC offers organizations with the ability protect employees from data breaches with personal HEROIC accounts and resources to properly protect them.

Penetration Testing
Penetration testing can help determine whether your system is vulnerable to attack if current defenses are sufficient and which defenses (if any) were defeated.
Regulatory Compliance
Our cybersecurity analysts help organizations understand which regulations, policies and requirements need to be met in order to become compliant.
Benefits of Penetration Testing
& Risk Assessments
Detect and manage vulnerabilities
A penetration test (or pen test) assesses an organization’s current security measures and ability to defend its applications, networks, users and endpoints from unapproved access to protected assets. Pen tests confirm threats posed by security vulnerabilities and/or faulty processes, which then allow IT personnel and security experts to intelligently prioritize remediation and apply needed security patches. Organizations should routinely conduct pen tests and risk assessments to more efficiently anticipate security threats facing crucial information and critical systems.
Establish compliance and evade penalties
Organizations are expected to abide by various requirements when handling customer data. Conducting penetration tests stops organizations from incurring penalties and fines. Some national laws or well known certifications (e.g. ISO27001, PCI DSS, HIPPA) require organizations to perform penetration tests against their information systems to make sure proper security measures are in place and compliance is met.
Avoid downtime and data breach expenses
A security breach can be very expensive to recover from. Recovery may include IT remediation, customer protection, legal activities, public relations efforts, reduced revenues, penalties, and even decrease in employee performance. Penetration testing helps organizations avoid possible financial setbacks and expenses by proactively detecting and addressing security threats before a breach or attack occurs. It’s always better for a business to proactively maintain its security than to face extreme losses.
Protect customer loyalty and company image
Compromised customer data can destroy a company’s brand and negatively impact its bottom line. Unfortunately, negative news gets out one way or another. Penetration testing helps an organization avoid data incidents that may put the organization’s reputation and reliability at stake. By conducting frequent pen tests and risk assessments, organizations establish a culture of trust that is then shared to customers. Showing that data security is top of mind speaks volumes to customer bases and the market as a whole.