
Bilddagboken
Breach Details
Description
We often see older breaches resurface in credential stuffing attacks or aggregated data dumps, but the Bilddagboken breach from 2008 caught our eye due to its deceptive simplicity. It lacks the standard PII we're accustomed to, like emails or passwords. Instead, this breach is a stark reminder of the long tail of data security and the potential for seemingly innocuous data to be weaponized years later. The data had been quietly circulating in various archives, but we noticed a recent uptick in mentions on several underground forums, specifically related to identity verification services. What struck us wasn't the volume of records, but the persistence of the data and its potential use in more sophisticated social engineering attacks.
The Old Blog Platform with Lingering Risk
The Bilddagboken breach, dating back to January 1, 2008, involved the exfiltration of data from the then-popular Swedish blogging platform. While the breach itself is not new, its continued availability and potential for misuse warrant attention. The absence of traditional credentials like emails and passwords might lead some to dismiss it, but the platform hosted personal blogs and online journals – a goldmine of personal details, writing styles, and social connections. The resurgence of interest in this breach highlights the need to consider the cumulative risk of seemingly harmless data points. This incident serves as a cautionary tale about data retention and the evolving threat landscape.
Breach Stats:
* Total records exposed: **10,536**
* Types of data included: None (but included blog posts, user profiles, social connections)
* Sensitive content types: Personal narratives, social interactions, potentially PII within blog posts
* Source structure: Database
* Leak location(s): Various online archives and underground forums
External Context & Supporting Evidence
While direct coverage of the 2008 Bilddagboken breach is scarce, its impact can be inferred from broader discussions about data privacy and security. The incident aligns with the trend of older breaches resurfacing in new contexts, as highlighted in numerous threat reports. The lack of immediate identifiable information doesn't negate the risk; instead, it shifts the focus to the potential for using the data to build detailed profiles for social engineering or identity theft. One Telegram post claimed the files were useful for "analyzing writing styles and identifying potential targets for phishing campaigns."
Leaked Data Types
None
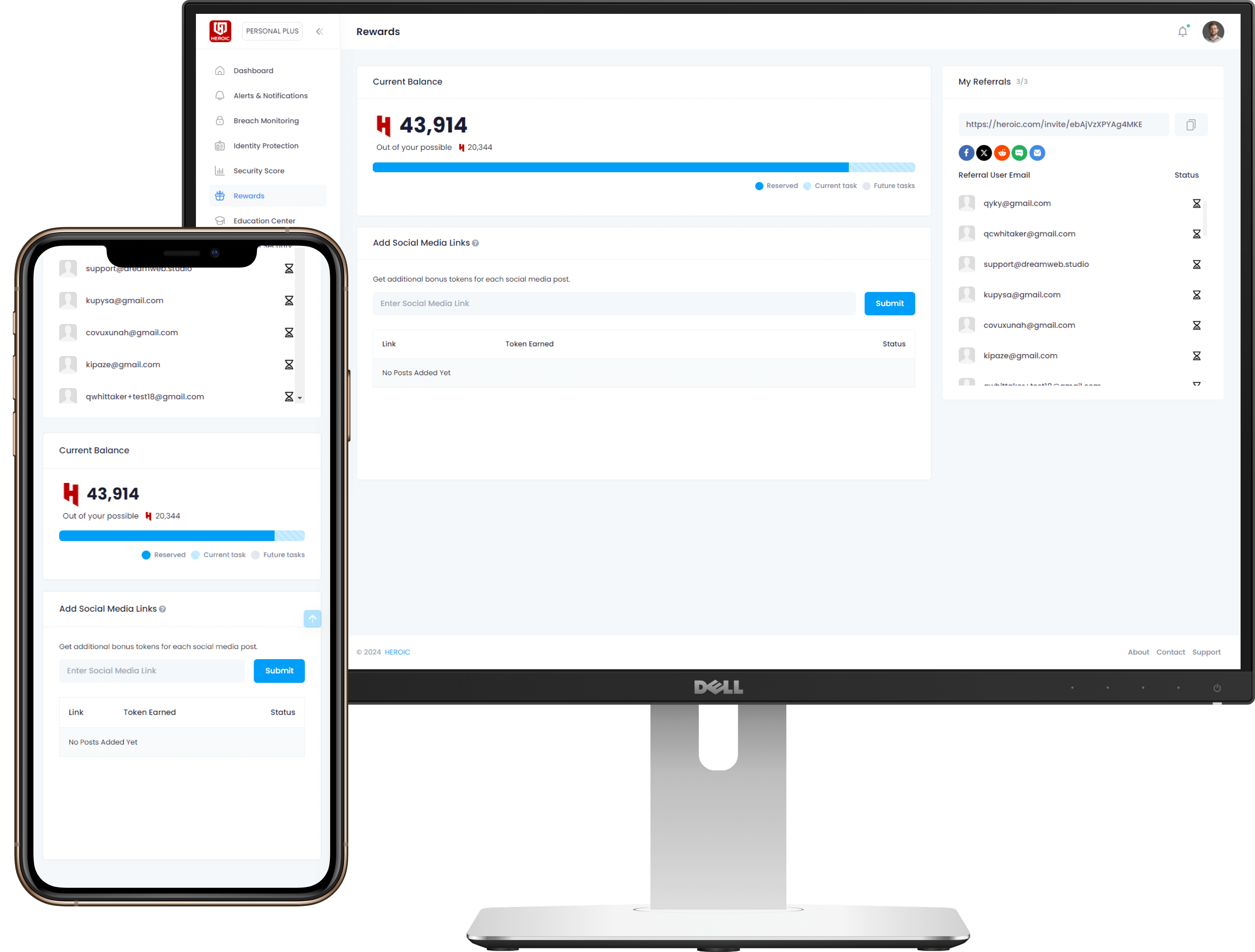
Get Early Access to the Guardian Platform
HEROIC is close to launching our next-generation platform where you can search, secure, and monitor all of your identities. To be the first in line, simply insert your email and you'll be added to the list

Be the first to know when we launch
Sign Up for Our Newsletter
Email marketing by Interspire



/qr-code.png)