
Deathly Souls
Breach Details
Description
We've been tracking a concerning rise in breaches originating from older, less-maintained online gaming communities. These platforms, often running outdated software and lacking robust security measures, present easy targets for opportunistic attackers. What really struck us about the recent Deathly Souls breach wasn't the number of accounts affected, but the age of the data and the fact that it's still circulating actively in underground forums. This indicates a long-term vulnerability and the potential for password reuse across other, more critical services.
The Deathly Souls Leak: 15,313 Accounts Resurfaced
The breach, originating from March 19, 2012, involved the compromise of the Deathly Souls gaming community database. This leak has resurfaced recently in several dark web forums, highlighting the enduring risk posed by older data breaches. The compromised data includes 15,313 user accounts, exposing usernames, email addresses, IP addresses, hashed passwords, and hash types. The age of this breach makes it particularly relevant, as users may have reused these credentials on other platforms over the past decade.
The breach first came to our attention when we observed mentions of a Deathly Souls database dump on a popular breach aggregation forum. The poster offered the data for free, claiming it was "old but still juicy" due to the potential for credential stuffing attacks against other gaming and online service accounts. The reappearance of this data underscores the persistent threat from legacy breaches and the need for continuous monitoring of exposed credentials.
This breach matters to enterprises because it illustrates the long tail of data security risk. Even breaches from over a decade ago can still pose a threat if users have reused passwords across multiple accounts. The gaming sector is often targeted for its user data, which can be valuable for identity theft and fraud. This incident also highlights the need for organizations to implement robust password management policies and multi-factor authentication to mitigate the risk of credential reuse.
Breach Stats
Key point: Total records exposed: 15,313
Key point: Types of data included: IP Address, Hash Type, Email Address, Username, Passwords
Key point: Sensitive content types: User credentials
Key point: Source structure: Database
Key point: Leak location(s): Dark web forums
Key point: Date leaked: 19-Mar-2012
External Context & Supporting Evidence
While the Deathly Souls breach itself didn't garner significant mainstream media attention at the time, the broader trend of gaming community breaches is well-documented. Sites like HaveIBeenPwned have tracked numerous similar incidents, emphasizing the ongoing risk to users of online gaming platforms. The reappearance of this older data aligns with the growing prevalence of credential stuffing attacks, where attackers use previously compromised credentials to gain unauthorized access to other accounts. Security researchers have noted a significant increase in these types of attacks in recent years, often fueled by the availability of older breach data. One Telegram post claimed the files were "a good start for cracking passwords."
Leaked Data Types
Ip · Address · Hash · Type · Email · Username · Passwords
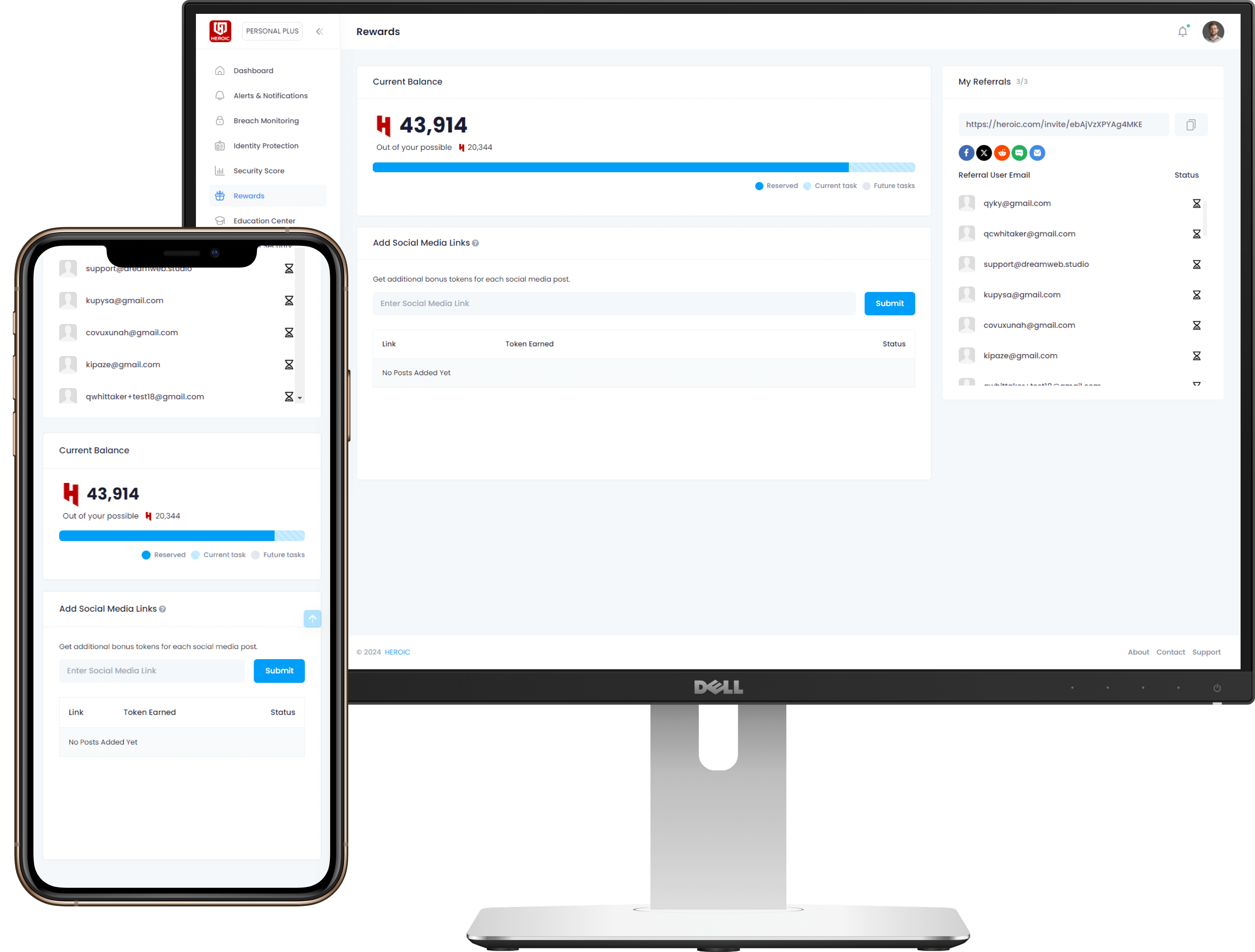
Get Early Access to the Guardian Platform
HEROIC is close to launching our next-generation platform where you can search, secure, and monitor all of your identities. To be the first in line, simply insert your email and you'll be added to the list

Be the first to know when we launch
Sign Up for Our Newsletter
Email marketing by Interspire



/qr-code.png)