
Emlog_cn_gp
Breach Details
Description
We've been tracking a worrying trend of older database dumps resurfacing in new contexts, often repackaged to target specific sectors. This week, our team noticed a spike in mentions of an old Emlog_cn_gp database leak from July 2011. What struck us wasn't the size of the breach – with just over 14,000 records, it's relatively small – but rather the aggressive marketing around it, specifically targeting Chinese-speaking developers and web hosting providers. The data had been circulating quietly for years, but its recent repackaging and promotion suggest a renewed interest in exploiting it for credential stuffing or targeted attacks.
Emlog_cn_gp: The Resurfaced 2011 Database of 14,000 Users
The Emlog_cn_gp database, originating from a Chinese-language blogging platform, resurfaced with increased visibility in late October 2024. While the initial breach occurred in July 2011, its recent rediscovery and repackaging on underground forums caught our attention. The database contains 14,012 records, primarily consisting of usernames and salted MD5 password hashes. The leak's re-emergence coincides with a broader trend of attackers leveraging older, forgotten breaches for credential stuffing and account takeover attacks. This is particularly concerning for organizations that may have employees or customers who used the Emlog_cn_gp platform or similar services with weak password reuse habits.
Breach Stats:
* Total records exposed: 14,012
* Types of data included: Usernames, salted MD5 password hashes
* Source structure: Database dump
* Leak location(s): Various hacking forums and Telegram channels
The renewed interest in this older breach aligns with a wider pattern. As reported by BleepingComputer, attackers are increasingly targeting older, less-protected databases to find credentials that can be reused on more valuable targets. The relatively small size of the Emlog_cn_gp leak might make it seem insignificant, but its value lies in the potential for password reuse across different platforms, a common vulnerability exploited by attackers. One Telegram post we observed advertised the database as a "goldmine for password spraying," highlighting the intended use of the data.
Leaked Data Types
None
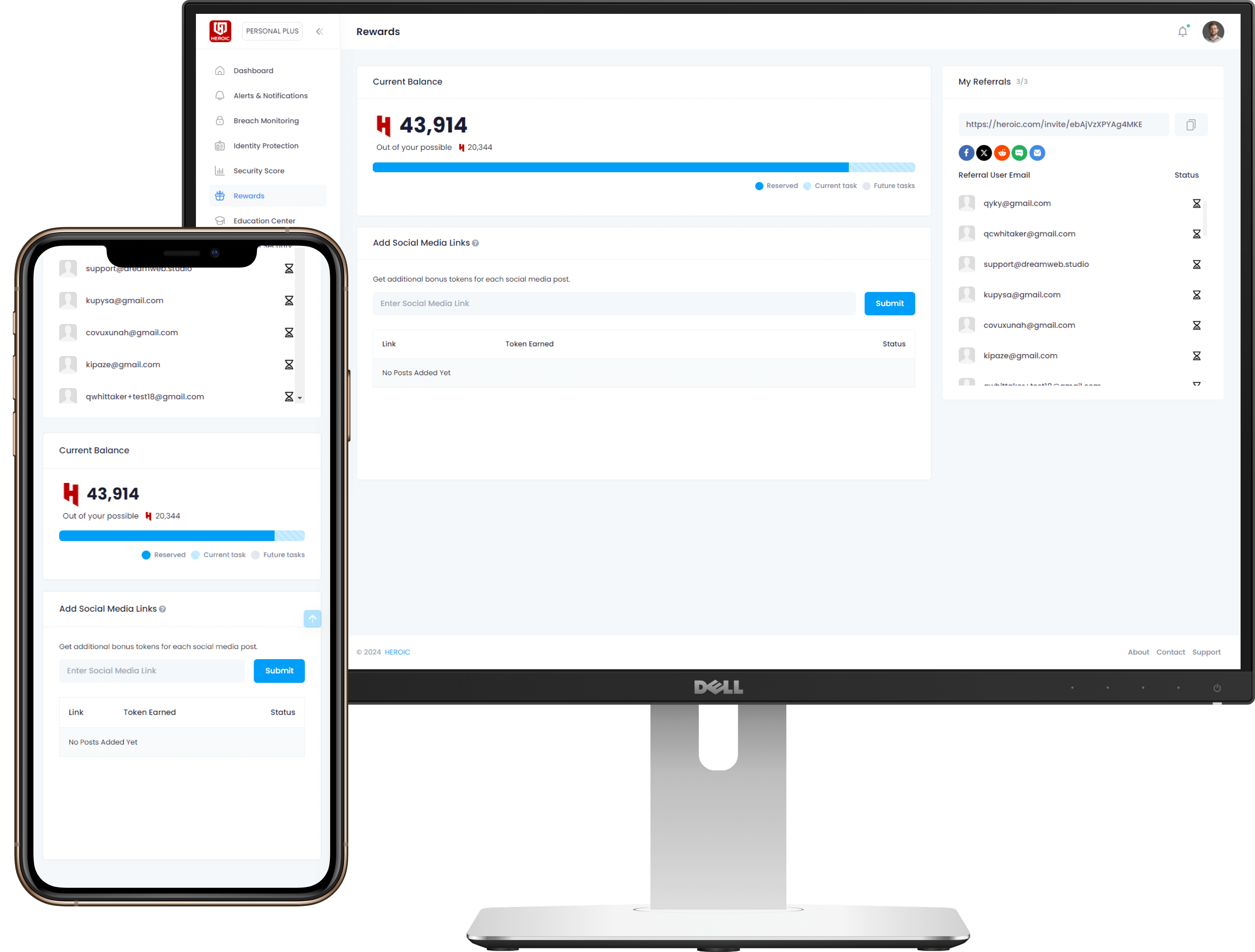
Get Early Access to the Guardian Platform
HEROIC is close to launching our next-generation platform where you can search, secure, and monitor all of your identities. To be the first in line, simply insert your email and you'll be added to the list

Be the first to know when we launch
Sign Up for Our Newsletter
Email marketing by Interspire



/qr-code.png)