
FC Zenit ru
Breach Details
Description
We've been tracking an uptick in older database leaks surfacing on various hacking forums, often re-packaged and sold as "new" data. What caught our attention wasn't the size of this particular leak, but its age and the specific hashing algorithm used. The FC Zenit ru database, dating back to July 2010, utilizes the outdated DES_MD5 hashing algorithm, making password cracking relatively straightforward with modern tools. This highlights the long tail of legacy security vulnerabilities and the continued risk they pose, even years after the initial breach may have occurred.
The FC Zenit Breach: 84K User Credentials Exposed from 2010
This breach involves a database associated with FC Zenit, a Russian professional football club. The exposed data consists of 84,334 user records. While the leak itself is not new, its re-emergence and the weak hashing algorithm employed present a significant risk. The database appears to be a direct export, likely from a compromised server dating back over a decade.
The data was first observed on a popular hacking forum on October 26, 2024. The poster advertised it as a "fresh" database, attempting to capitalize on its perceived novelty. What makes this leak noteworthy for enterprise security teams is not the initial compromise, but the potential for credential stuffing attacks. Users who registered on the FC Zenit ru website in 2010 may have re-used those credentials on other platforms, including corporate accounts. The weak DES_MD5 hashing further amplifies the risk, allowing attackers to easily recover plaintext passwords.
This incident underscores the enduring threat posed by older breaches and the importance of proactive credential monitoring. The use of outdated hashing algorithms is a common characteristic of older leaks, making them particularly vulnerable to cracking. This breach fits into the broader trend of threat actors targeting older, less-protected databases for easy access to credentials.
Key point: Total records exposed: 84,334
Key point: Types of data included: Usernames, passwords (hashed with DES_MD5)
Key point: Sensitive content types: Potentially reused passwords
Key point: Source structure: Likely a database export
Key point: Leak location(s): Hacking forum (specific URL available upon request)
Key point: Date of first appearance: October 26, 2024
External Context & Supporting Evidence
While mainstream media hasn't covered this specific re-emergence, the broader issue of password reuse and the dangers of weak hashing algorithms are well-documented. Security researcher Troy Hunt's Have I Been Pwned? database is a valuable resource for checking if your email address or password has been compromised in known breaches. The OWASP (Open Web Application Security Project) also provides extensive guidance on password security and the importance of using strong hashing algorithms.
On various hacking forums, discussions surrounding the FC Zenit ru database have been minimal, likely due to its age and the fact that the data has been circulating for some time. However, some users have noted the ease with which the passwords can be cracked, highlighting the vulnerability created by the use of DES_MD5. One user on the forum stated, "These DES hashes are like butter. Takes longer to download the file than to crack the passwords."
Leaked Data Types
None
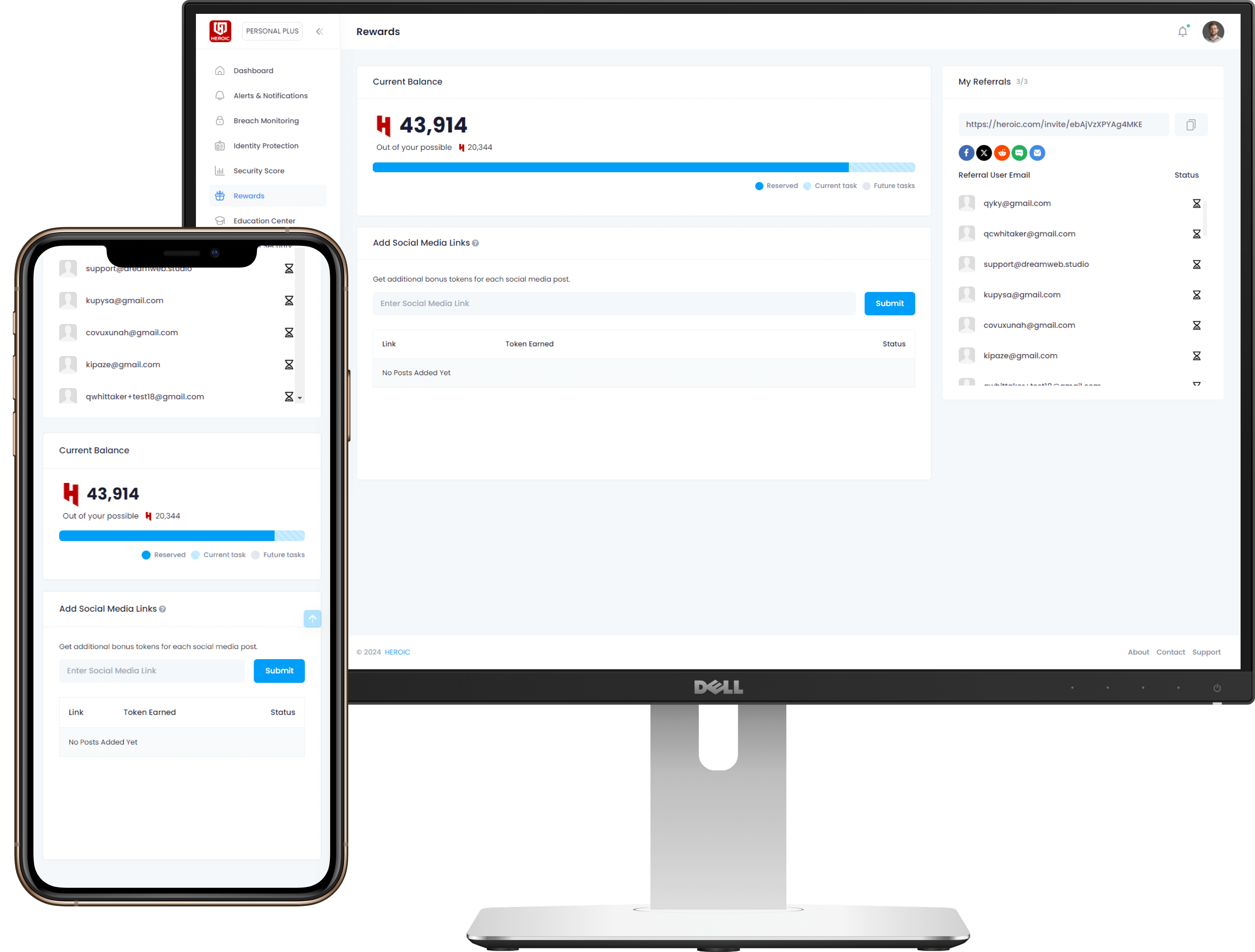
Get Early Access to the Guardian Platform
HEROIC is close to launching our next-generation platform where you can search, secure, and monitor all of your identities. To be the first in line, simply insert your email and you'll be added to the list

Be the first to know when we launch
Sign Up for Our Newsletter
Email marketing by Interspire



/qr-code.png)