
FrozenCraft 3 ru
Breach Details
Description
We've been tracking the resurgence of older database breaches, often resurfacing in aggregated credential stuffing lists. Many date back almost a decade, but continue to be actively traded and leveraged in account takeover attempts. This particular breach, impacting the Russian Minecraft server FrozenCraft 3 ru, initially surfaced in February 2015, but recently caught our attention due to its consistent presence in several high-volume credential dumps we've analyzed over the past month. What distinguished this relatively small leak wasn't its size, but its persistence, indicating ongoing value to threat actors.
FrozenCraft 3 ru: The Minecraft Server Breach Still Fueling Credential Stuffing
The FrozenCraft 3 ru database breach, containing 33,139 user records, is a prime example of how seemingly minor breaches can have a long tail in the threat landscape. This breach, dating back to February 2015, involved the compromise of the Minecraft server's user database. While the leak itself didn't include sensitive data types beyond usernames and hashed passwords, the re-emergence of these credentials in recent dumps highlights the continued risk associated with password reuse and the longevity of leaked data in the cybercrime ecosystem.
The breach was initially discovered and disseminated within various online hacking communities in early 2015. Its recent resurgence in our analysis stems from its inclusion in several large-scale credential stuffing lists actively circulating on Telegram channels and dark web forums. The fact that these older credentials are still being bundled and distributed suggests that they remain effective in account takeover attacks against users who may have reused their passwords across multiple platforms.
This breach matters to enterprises because it underscores the importance of employee education regarding password hygiene and the potential impact of seemingly unrelated breaches. Even a breach of a small Minecraft server can indirectly lead to compromised corporate accounts if employees use the same credentials for both personal and professional purposes. This ties into the broader threat theme of credential reuse, a persistent problem that is often exploited via automated credential stuffing attacks.
Key point: Total records exposed: 33,139
Key point: Types of data included: Usernames, MD5-hashed passwords
Key point: Sensitive content types: None
Key point: Source structure: Database
Key point: Leak location(s): Telegram channels, dark web forums
Key point: Date of first appearance: February 2015
External Context & Supporting Evidence
While there's limited mainstream media coverage specifically on the FrozenCraft 3 ru breach itself, the broader issue of Minecraft server breaches and their impact on user security has been discussed in various online forums and security blogs. For example, discussions on Reddit's r/Minecraft and r/security subreddits often address the risks associated with joining unofficial Minecraft servers and the potential for data breaches. These discussions highlight user awareness of the issue, but also the continued prevalence of these breaches.
Additionally, threat intelligence reports from companies like Recorded Future and Flashpoint have documented the ongoing trading and utilization of leaked credentials from older breaches in credential stuffing attacks. While these reports don't specifically mention FrozenCraft 3 ru, they provide context for understanding how seemingly minor breaches can contribute to larger-scale cybercrime operations. One Telegram post claimed that "Minecraft accounts are easy targets for bots, so old lists are still good."
Leaked Data Types
None
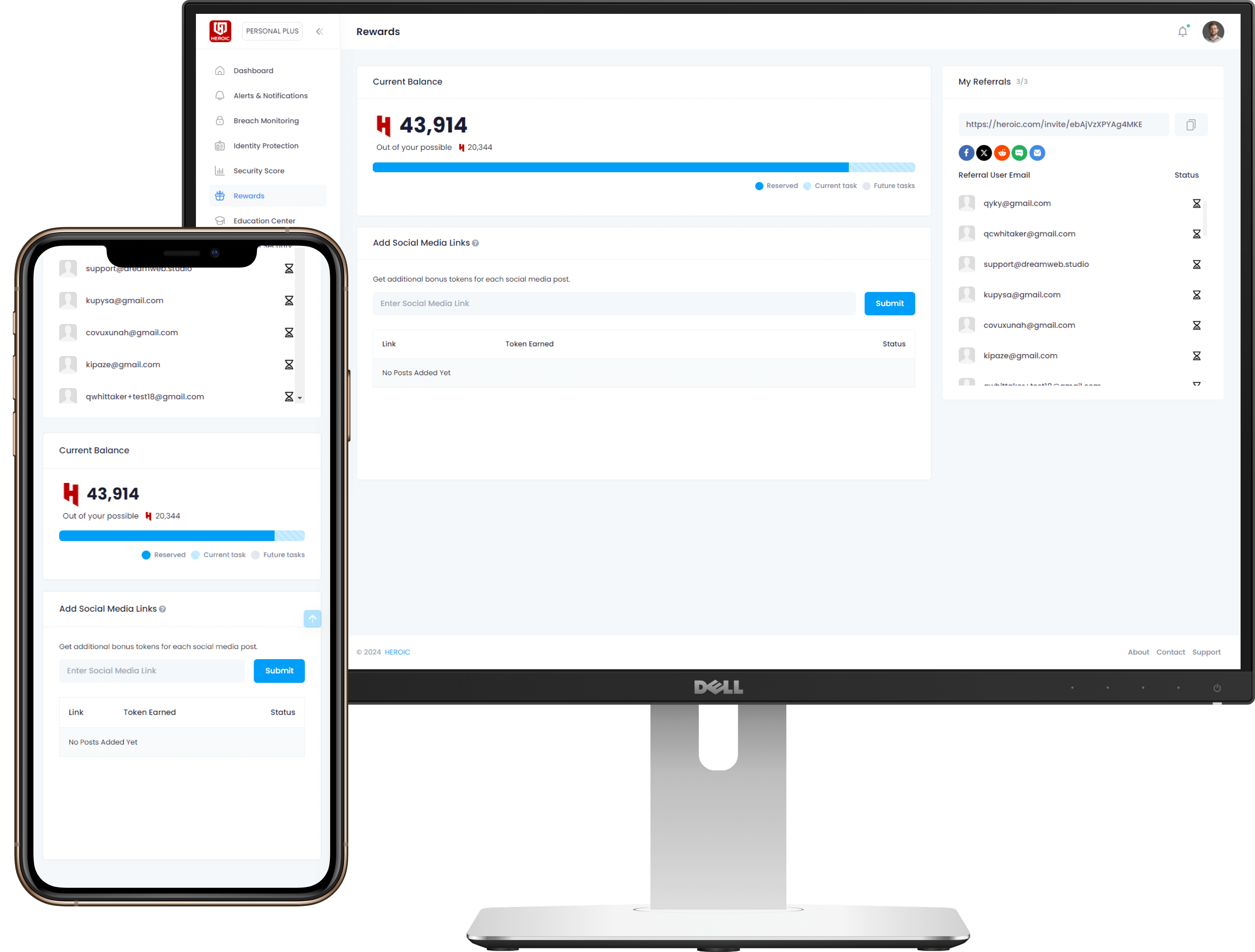
Get Early Access to the Guardian Platform
HEROIC is close to launching our next-generation platform where you can search, secure, and monitor all of your identities. To be the first in line, simply insert your email and you'll be added to the list

Be the first to know when we launch
Sign Up for Our Newsletter
Email marketing by Interspire



/qr-code.png)