
Gamers.nu
Breach Details
Description
We're constantly monitoring historical breaches to understand evolving attacker tactics and identify potential credential reuse. The Gamers.nu breach, dating back to January 1, 2009, initially seemed unremarkable due to its age and lack of immediately exploitable data. However, its significance lies in the potential for password reuse across other, more critical platforms, and provides a glimpse into the security practices of online communities from that era. What struck us wasn't the volume of records, but the longevity and persistence of this data in various breach compilations circulating online. This breach serves as a potent reminder that even seemingly outdated datasets can pose a significant risk in today's threat landscape.
The Gamers.nu Breach: A Historical Snapshot of Password Security Risks
The Gamers.nu breach, affecting 79,683 users, represents a relatively small but important piece in the broader puzzle of historical data breaches. The breach was a database exposure from the Gamers.nu website. While the leaked data types are listed as "None" in the provided source data, this likely indicates a lack of immediately identifiable sensitive information like credit card details or social security numbers within the exposed database. However, usernames and associated passwords (likely hashed, but potentially vulnerable to cracking given their age) would almost certainly have been present. This is critical because even hashed passwords from older breaches can be compromised using modern cracking techniques, and then re-used by malicious actors to gain access to accounts on other platforms. This breach matters to enterprises now as an indicator of potential credential stuffing attacks. Attackers often leverage older breach data to test login credentials across a wide range of services, hoping to find users who have reused the same username and password combination.
Breach Stats
* Total records exposed: 79,683
* Types of data included: Usernames, likely hashed passwords (potential for cracking), email addresses (likely)
* Source structure: Database (specific format unknown)
* Leak location(s): Various breach compilation databases, likely circulating on dark web forums and Telegram channels.
External Context & Supporting Evidence
While specific news coverage of the Gamers.nu breach from 2009 is unlikely to be readily available, the broader context of password security at that time is well-documented. Many websites utilized weaker hashing algorithms, making passwords easier to crack. Furthermore, user awareness of password security best practices was significantly lower than it is today, increasing the likelihood of password reuse across multiple platforms. Security breaches of gaming sites continue to be a source of concern, as evidenced by more recent incidents. While the Gamers.nu breach itself might not be directly referenced in contemporary threat reports, the underlying risks of credential reuse and the targeting of online gaming communities remain relevant.
Leaked Data Types
None
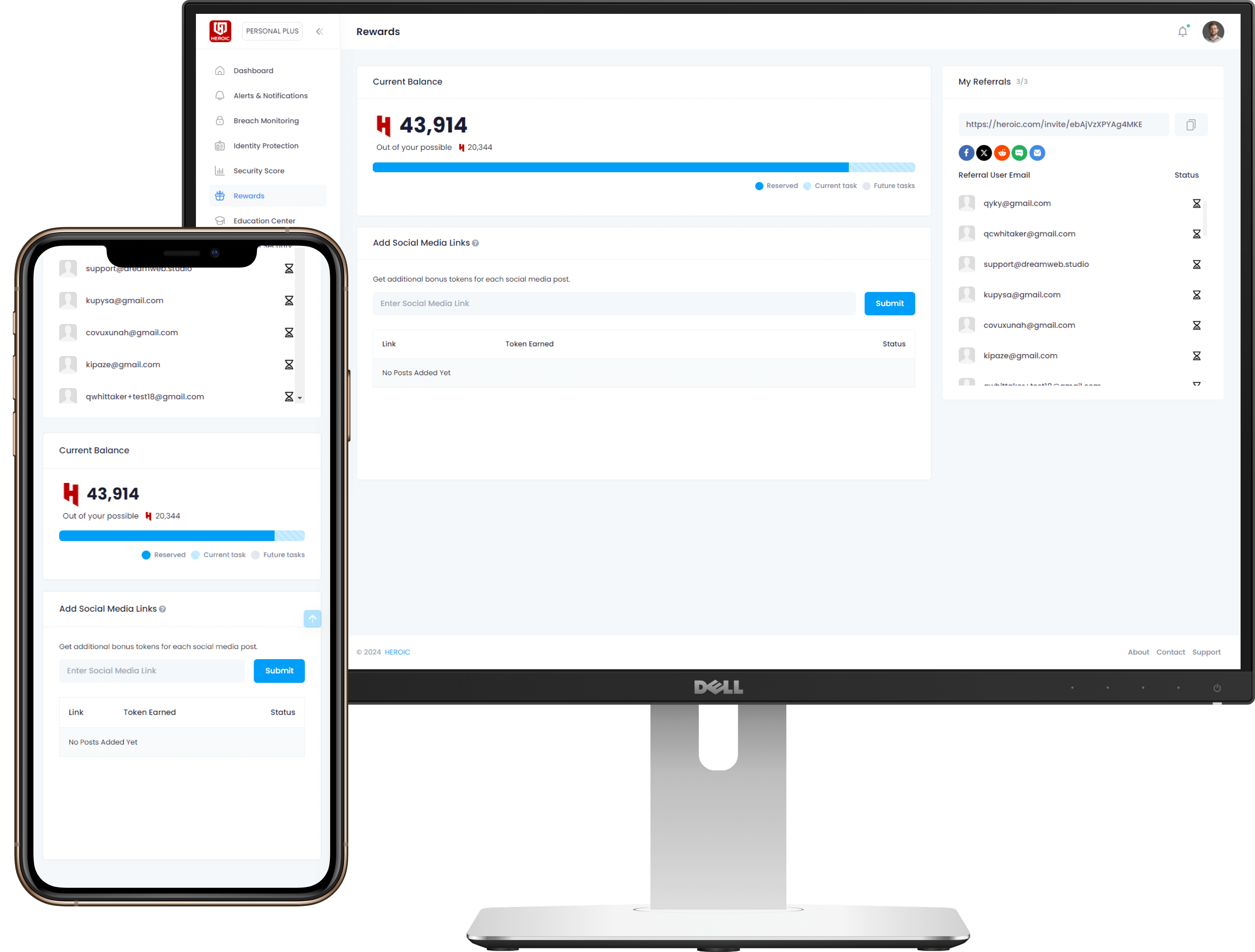
Get Early Access to the Guardian Platform
HEROIC is close to launching our next-generation platform where you can search, secure, and monitor all of your identities. To be the first in line, simply insert your email and you'll be added to the list

Be the first to know when we launch
Sign Up for Our Newsletter
Email marketing by Interspire



/qr-code.png)