
JetAudio
Breach Details
Description
We've been tracking a resurgence of older breaches being re-packaged and sold on various dark web forums, often targeting individuals who may have reused credentials across multiple platforms. What really struck us about this particular incident wasn't the size of the breach itself, but the age and the specific user demographic it likely impacts. It serves as a stark reminder that data from even seemingly insignificant breaches can resurface years later, posing ongoing risks to individuals and potentially serving as stepping stones for broader attacks. The age of the breach also highlights the persistence of older hashing algorithms and the vulnerabilities they present.
JetAudio Forum Breach: 17,500 User Records Resurface After 15 Years
A data breach impacting the forum website of JetAudio, an audio software company owned by COWON, initially occurred in November 2008. The breach, affecting approximately 17,500 users, has recently resurfaced on multiple dark web marketplaces. The data includes sensitive user information, making it a potential threat to individuals who may have reused credentials on other platforms.
The breach was initially reported in various security circles shortly after it occurred in 2008. It caught our attention now due to its reappearance on a prominent Telegram channel known for aggregating and selling older breach data. The age of the breach, coupled with the type of data exposed, suggests that many affected users may not be aware of the compromise or have taken appropriate remediation steps. This makes them potentially vulnerable to credential stuffing attacks and other forms of identity theft.
The re-emergence of this data highlights the long-term risks associated with data breaches and the importance of proactive security measures, including unique password generation and monitoring for compromised credentials. The breach is also a reminder of the need to phase out older, less secure hashing algorithms used to store passwords.
Key point: Total records exposed: 17,542
Key point: Types of data included: Email addresses, usernames, password hashes (vBulletin), IP addresses, dates of birth
Key point: Sensitive content types: PII (personally identifiable information)
Key point: Source structure: Database export (likely SQL)
Key point: Leak location(s): Telegram channels, dark web forums
Key point: Date of first appearance: November 2008 (initial breach), resurfaced in late 2023/early 2024
External Context & Supporting Evidence
While the original breach received limited mainstream media coverage at the time, its existence is documented in various online breach databases and security forums. A search reveals entries on sites like "Have I Been Pwned?" confirming the scope and nature of the compromised data. The use of vBulletin hashes is particularly noteworthy, as these have been subject to numerous cracking attempts over the years due to known vulnerabilities in the algorithm and the availability of rainbow tables.
The practice of re-selling older breaches is increasingly common, as threat actors seek to monetize previously compromised data. This trend is fueled by the assumption that many users will not have changed their passwords since the original breach, making the data still valuable for credential stuffing and account takeover attacks. One Telegram post observed by our team advertised the JetAudio data alongside several other older breaches, claiming they were "freshly updated and verified" against current email lists.
Leaked Data Types
Email · Address · Password · Hash · Username · Ip · Birthday
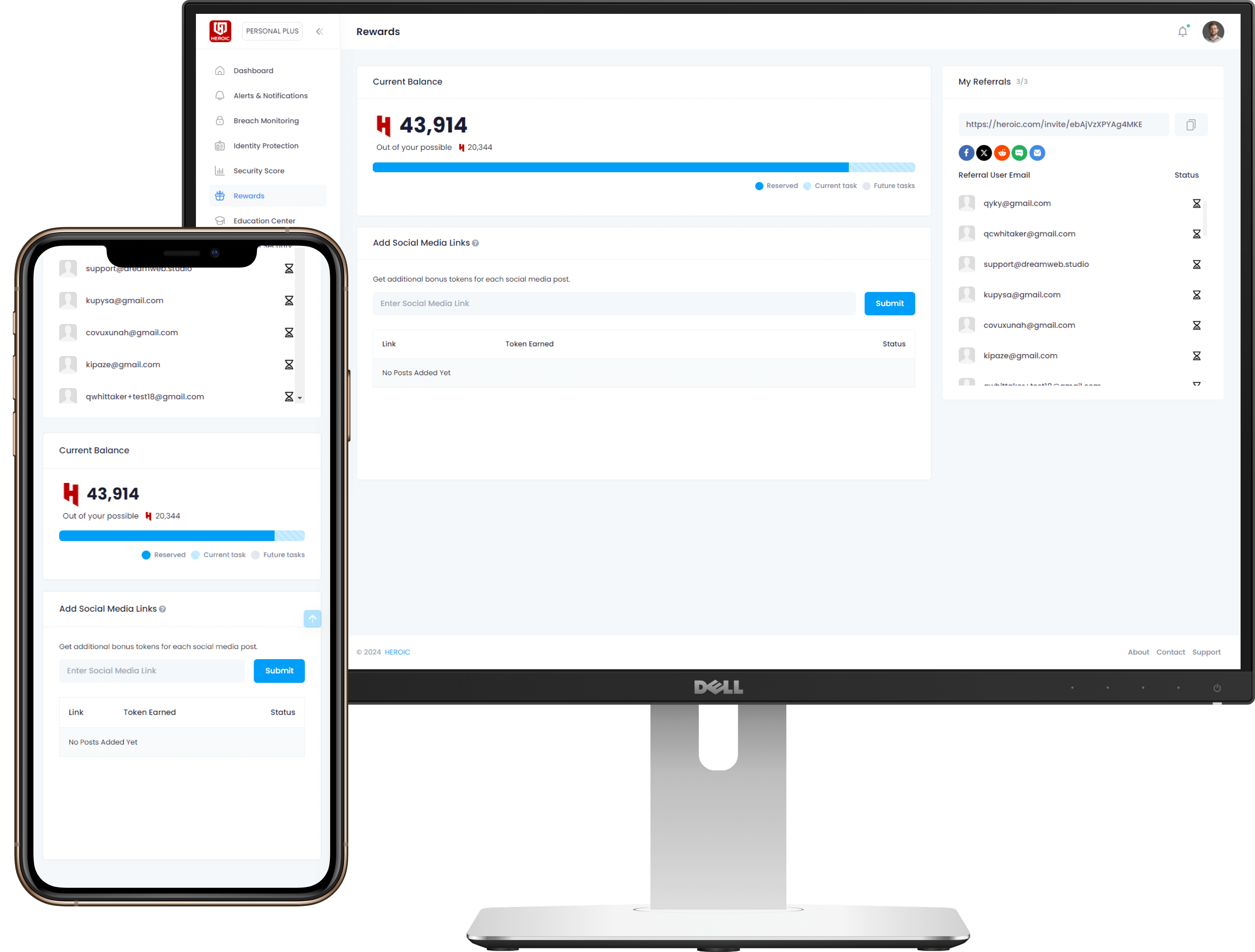
Get Early Access to the Guardian Platform
HEROIC is close to launching our next-generation platform where you can search, secure, and monitor all of your identities. To be the first in line, simply insert your email and you'll be added to the list

Be the first to know when we launch
Sign Up for Our Newsletter
Email marketing by Interspire




/qr-code.png)