
Last.fm
Breach Details
Description
We often see older breaches resurface, but the Last.fm data dump caught our eye due to its sheer size and the continued reliance on unsalted MD5 hashing algorithms, even in 2012. The data had been circulating in smaller circles for a while, but we noticed a significant uptick in its availability on various dark web forums and Telegram channels recently. What really struck us wasn't just the volume of credentials, but the potential for password reuse across other platforms, given the age of the breach and the likelihood that many users haven't updated their passwords since.
Last.fm's 2012 Breach: 33 Million Accounts Resurface
The Last.fm breach, originally occurring in March 2012, exposed over 33 million user accounts. While the company acknowledged a security incident at the time, the full extent of the breach wasn't known until the data was publicly released in September 2016. The resurgence of this data now presents a renewed risk for credential stuffing attacks and account takeovers.
The breach initially caught attention when the database was offered for sale on a dark web forum dedicated to selling large-scale data dumps. What made this particular leak stand out was the inclusion of a substantial number of unique email addresses coupled with poorly secured passwords. The data had been quietly traded among threat actors, but its recent widespread availability significantly increases the risk to individuals and organizations.
This breach matters to enterprises now because many users likely reused their Last.fm passwords on other platforms, including corporate accounts. This highlights the long-tail risk associated with older breaches and the importance of continuous monitoring for compromised credentials. The use of unsalted MD5 hashing, a practice considered outdated and insecure even in 2012, further exacerbates the problem. This incident ties into the broader threat theme of credential reuse and the ongoing exploitation of legacy security vulnerabilities.
Key point: Total records exposed: 33,523,283
Key point: Types of data included: Email Addresses, Usernames, Passwords (unsalted MD5 hashes)
Key point: Sensitive content types: Potentially PII due to password reuse across multiple platforms.
Key point: Source structure: Database dump
Key point: Leak location(s): Various dark web forums, Telegram channels, and breach aggregation sites.
Key point: Date of first appearance: March 2012 (initial breach), September 2016 (public release), recent resurgence in 2024
External Context & Supporting Evidence
Security researcher Troy Hunt added the Last.fm breach to Have I Been Pwned? in 2016, allowing individuals to check if their email address was compromised. This demonstrates the long-standing awareness of the breach within the security community. News outlets, including ZDNet, covered the breach in 2016, highlighting the potential impact on users. The continued circulation of this data underscores the need for proactive security measures to mitigate the risks associated with credential compromise. One Telegram post claimed the files were "re-dumped, cleaned, and ready for cracking".
Leaked Data Types
Hash · Type · Email · Address · Username · Passwords
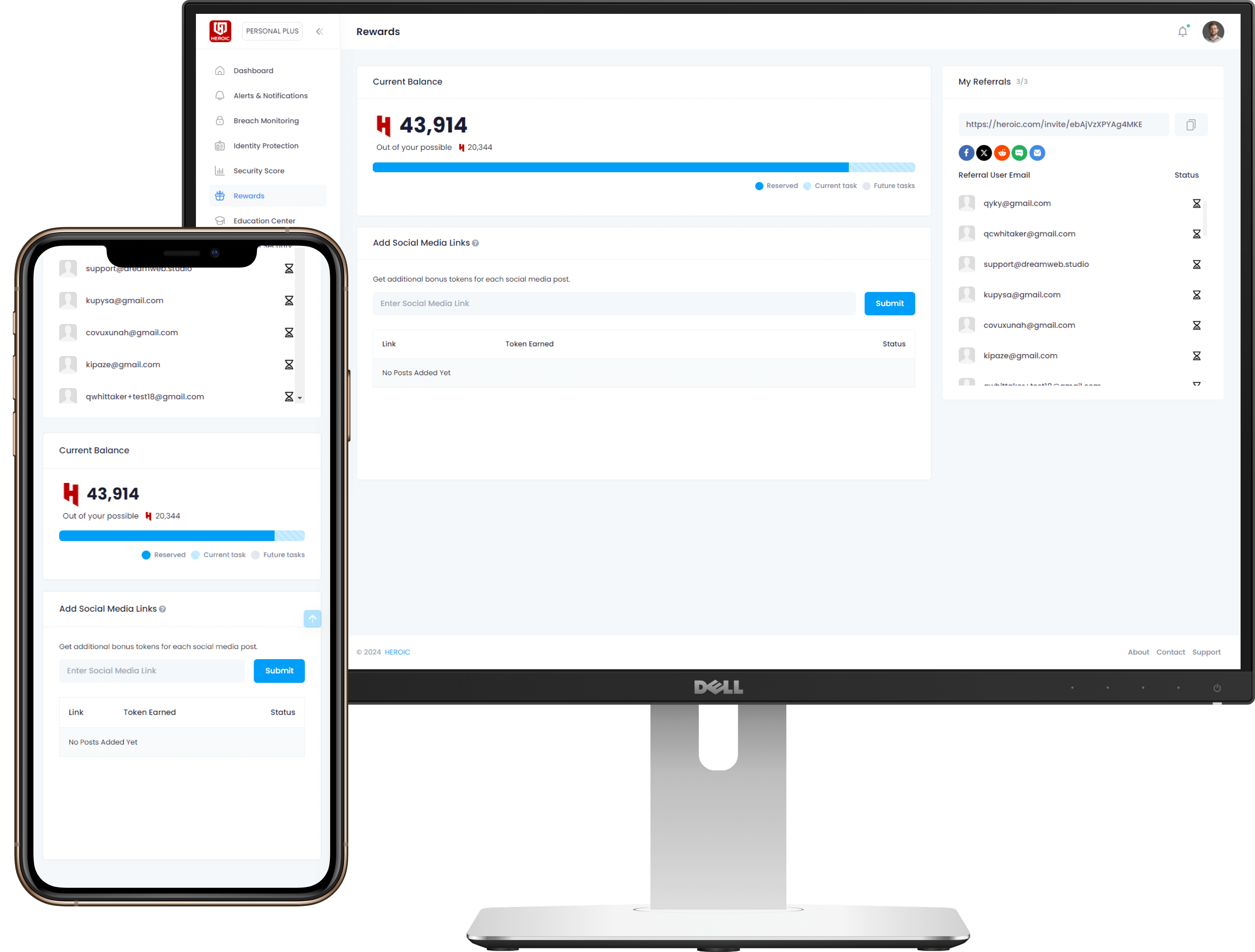
Get Early Access to the Guardian Platform
HEROIC is close to launching our next-generation platform where you can search, secure, and monitor all of your identities. To be the first in line, simply insert your email and you'll be added to the list

Be the first to know when we launch
Sign Up for Our Newsletter
Email marketing by Interspire



/qr-code.png)