
MilitarySingles
Breach Details
Description
We've been tracking the resurgence of older breach datasets as threat actors attempt to re-monetize them, often by combining them with more recent data. What caught our attention with the MilitarySingles breach wasn't just the age of the data – dating back to March 2012 – but the surprisingly complete profile information contained within each record. While older breaches are common, the combination of email addresses, usernames, IP addresses, phone numbers, full names, and password hashes creates a valuable resource for identity theft and targeted phishing campaigns, even a decade later. The fact that this data is tied to a dating site focused on military personnel amplifies the risk, given the potential for exploitation by foreign intelligence services or malicious actors seeking to compromise sensitive information.
MilitarySingles Breach: A Blast from the Past with Modern Implications
The MilitarySingles breach from 2012 has resurfaced recently in several dark web forums and Telegram channels known for trading older datasets. The breach, initially announced on Twitter by Operation Digiturk, involved a database dump containing a wealth of user information. The data's reappearance highlights the long tail of data breaches and the persistent threat posed by compromised credentials, even after many years.
The breach first gained notoriety after Operation Digiturk, an activist group, claimed responsibility and released the database. What made this breach particularly concerning was the comprehensive nature of the data exposed. Unlike breaches that only expose email addresses and passwords, this one included a wide array of personal information, making it more valuable for malicious actors. The re-emergence of this data allows attackers to cross-reference it with more recent breaches, potentially uncovering even more information about the individuals affected.
This breach matters to enterprises now because the compromised data can be used for highly targeted phishing attacks against military personnel and veterans. Attackers can leverage the personal information to craft convincing emails or social media messages, increasing the likelihood of successful compromise. The potential for identity theft and financial fraud is also significant, given the detailed profile information contained in the leaked database. Furthermore, the breach underscores the importance of regularly monitoring for compromised credentials and implementing robust security measures to protect sensitive data, even data that is considered "old." The fact that the data is tied to a dating site for military members makes it a prime target for social engineering attacks.
Key point: Total records exposed: 120,759
Key point: Types of data included: Email Address, Username, IP Address, Phone Number, First Name, Last Name, Password Hash
Key point: Sensitive content types: PII (Personally Identifiable Information)
Key point: Source structure: Database dump
Key point: Leak location(s): Dark web forums, Telegram channels
Key point: Date leaked: March 25, 2012 (initially), recently resurfaced
External Context & Supporting Evidence
While mainstream media coverage of the original MilitarySingles breach in 2012 was limited, mentions can be found in various security blogs and forums discussing historical data breaches. Discussions on security-focused Reddit communities also point to the continued circulation of this data. One Telegram post claimed the files were "useful for OSINT research on military personnel". The resurfacing of this breach aligns with a broader trend of threat actors targeting older datasets to maximize their value by combining them with more recent breaches and newly available tools for cracking password hashes.
Leaked Data Types
Email · Address · Username · Ip · Phone · Number · First · Name · Last · Password · Hash
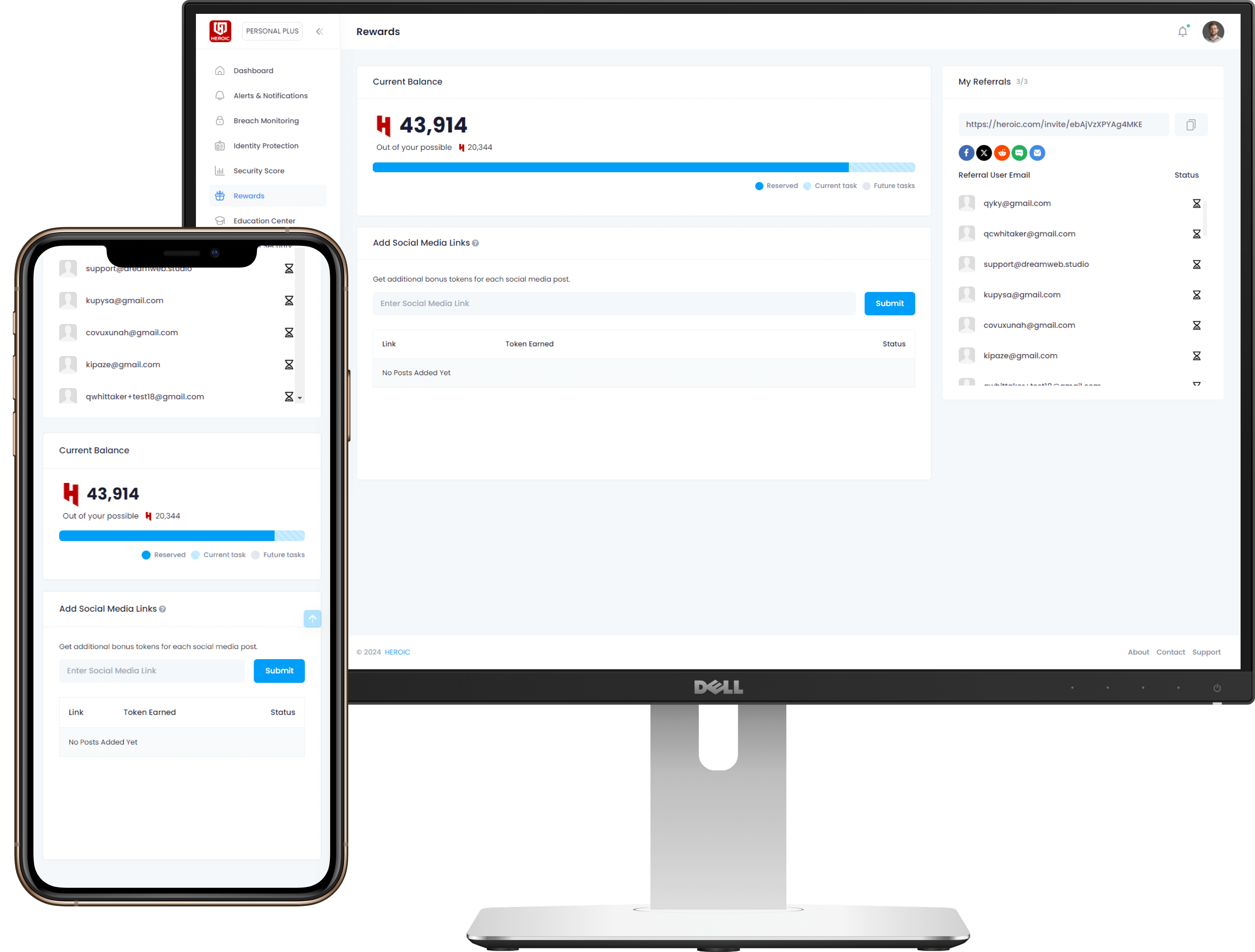
Get Early Access to the Guardian Platform
HEROIC is close to launching our next-generation platform where you can search, secure, and monitor all of your identities. To be the first in line, simply insert your email and you'll be added to the list

Be the first to know when we launch
Sign Up for Our Newsletter
Email marketing by Interspire



/qr-code.png)