
RuneHQ
Breach Details
Description
We've been tracking the resurgence of older database breaches circulating in underground forums, often repackaged and sold as "new" leaks to unsuspecting buyers. What caught our attention with the recent reappearance of the RuneHQ data wasn't the size – a relatively modest 11,369 records – but the age and persistent relevance of the data. Many users from communities around games like RuneScape reuse credentials across different platforms, meaning even a decade-old breach can still yield viable passwords for other services. The setup here felt different because it highlights the long tail of credential compromise and the enduring risk from legacy breaches.
RuneHQ Leak: A Decade-Old Breach Still Echoing
The RuneHQ breach, dating back to March 1, 2008, involved the compromise of a database containing 11,369 user records. The data includes sensitive information such as IP addresses, email addresses, usernames, and passwords, as well as information on the hash types used. This breach is noteworthy because of its age; the fact that these credentials are still circulating and potentially being used today is a testament to the enduring risk of password reuse and the slow pace of user remediation.
The breach was discovered after its re-emergence on several underground forums known for trading and sharing leaked databases. While the initial compromise occurred over a decade ago, the data continues to resurface, often repackaged and sold as a "new" leak. This highlights the need for continuous monitoring of leaked credential databases and proactive measures to identify and mitigate potential risks.
This breach matters to enterprises because it underscores the risk of credential stuffing attacks, where attackers use compromised credentials from one service to gain access to accounts on other platforms. Even if an organization's systems are secure, employees who reuse passwords may be vulnerable to attacks leveraging old leaks like this one. This incident ties into the broader threat theme of credential harvesting and the automation of attacks using leaked credentials.
Key point: Total records exposed: 11,369
Key point: Types of data included: IP Addresses, Email Addresses, Usernames, Passwords, Hash Type
Key point: Sensitive content types: PII
Key point: Source structure: Database
Key point: Leak location(s): Underground forums
Key point: Date of first appearance: 01-Mar-2008
External Context & Supporting Evidence
While specific news coverage of the original RuneHQ breach is limited due to its age, the incident aligns with broader reporting on the prevalence of credential stuffing attacks and the enduring risk of password reuse. Security experts like Troy Hunt (creator of Have I Been Pwned) have consistently highlighted the dangers of reusing passwords across multiple services, emphasizing that even old breaches can pose a significant threat.
Discussions on forums like Reddit's r/security and r/privacy often highlight user experiences with credential stuffing attacks, where individuals find their accounts compromised on various platforms due to the reuse of passwords exposed in older breaches. These discussions underscore the real-world impact of these types of leaks.
Leaked Data Types
Ip · Address · Hash · Type · Email · Username · Passwords
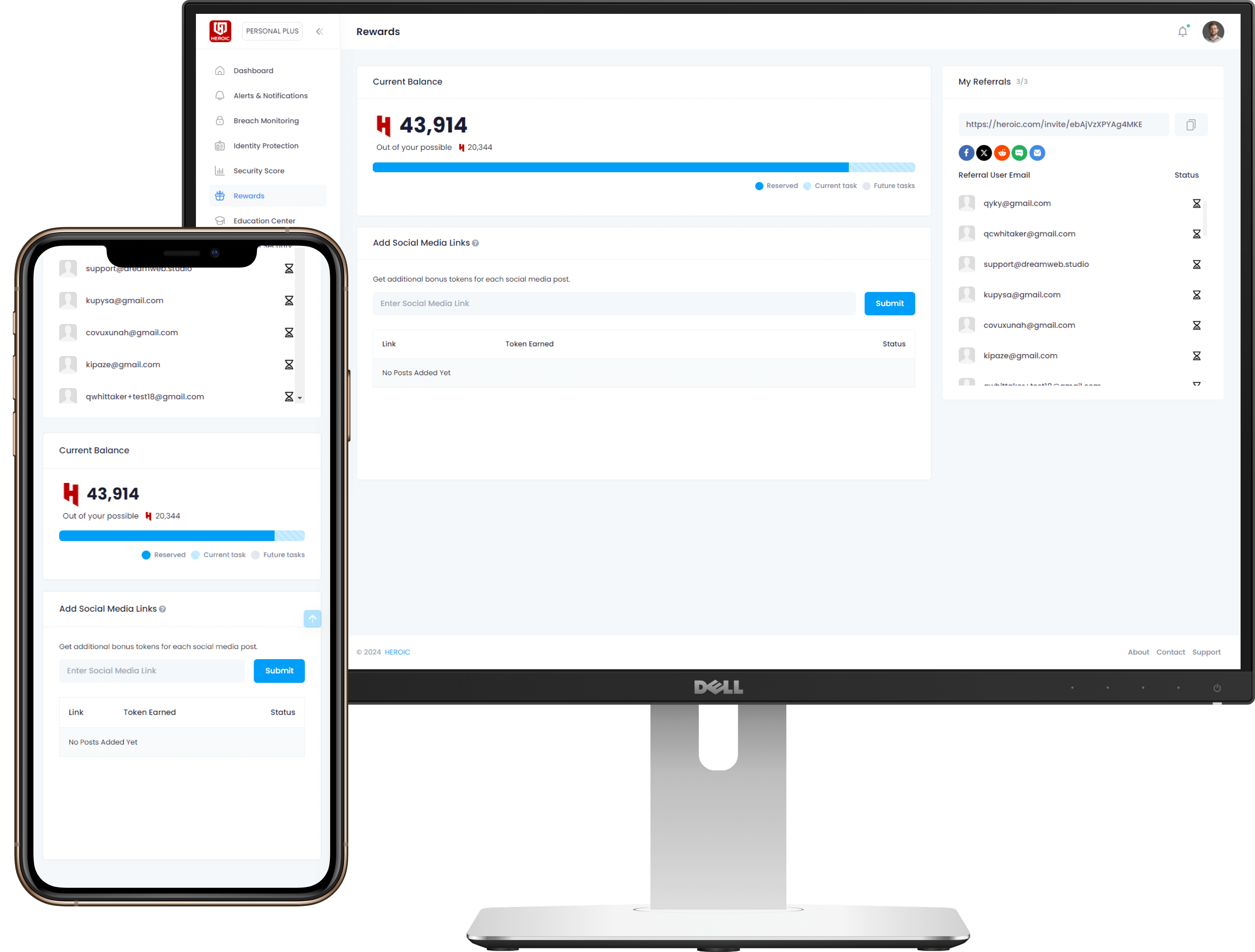
Get Early Access to the Guardian Platform
HEROIC is close to launching our next-generation platform where you can search, secure, and monitor all of your identities. To be the first in line, simply insert your email and you'll be added to the list

Be the first to know when we launch
Sign Up for Our Newsletter
Email marketing by Interspire



/qr-code.png)