
Social Engine Forum
Breach Details
Description
We've been tracking a resurgence in older forum database leaks, often resurfacing on Telegram channels catering to credential stuffing attacks. Many of these dumps are a decade old or more, but still contain valid, re-used passwords. What caught our attention with a recent Social Engine Forum database dump wasn't its size, but the cleartext passwords it contained, highlighting the security practices of the time and the continued risk they pose today. While the breach itself is old news, the data's reappearance in current threat landscapes makes it relevant for enterprises assessing their legacy password exposure.
Social Engine Forum Leak: Cleartext Passwords Re-emerge After a Decade
A database dump from Social Engine Forum, dating back to March 31, 2012, has resurfaced on multiple Telegram channels and dark web forums. The data contains a mix of information about users of the Social Engine Forum. This breach is not new, but its reappearance on platforms used for credential stuffing and account takeover attempts warrants renewed attention. The presence of cleartext passwords, coupled with older, weaker hashing algorithms, significantly increases the risk to individuals whose credentials may have been re-used across multiple services.
The breach initially occurred over a decade ago, but we observed its re-emergence on a Telegram channel known for aggregating and distributing leaked databases on [Date Redacted]. The data was posted with a brief description and a link to a downloadable archive. What made this stand out was the presence of a significant number of cleartext passwords, a stark contrast to modern security practices. The data also contained password hashes, but many used older, easily crackable algorithms. The combination of these factors makes the data particularly valuable for attackers.
This incident highlights the long-term risks associated with poor password security practices and the enduring value of older data breaches to attackers. Even though the breach is over a decade old, the exposed credentials can still be used in credential stuffing attacks against other platforms, especially if users haven't updated their passwords since 2012. This is particularly relevant for enterprises, as employees often re-use passwords across both personal and work accounts.
Key point: Total records exposed: 45,946
Key point: Types of data included: Email addresses, usernames, passwords (both cleartext and hashed), IP addresses, Hash Types
Key point: Sensitive content types: Email addresses, Passwords, IP Addresses, Usernames
Key point: Source structure: Database dump
Key point: Leak location(s): Telegram channels, dark web forums
Key point: Date of first appearance: March 31, 2012 (original breach), [Date Redacted] (re-emergence on Telegram)
External Context & Supporting Evidence
While specific news coverage of the original 2012 Social Engine Forum breach is limited, similar incidents involving older forum databases have been widely reported. For example, security researcher Troy Hunt maintains a database of breached websites at HaveIBeenPwned.com, which often includes entries for older forum breaches that continue to pose a risk. The re-emergence of these older breaches is often discussed on security-focused subreddits like r/netsec and r/privacy, where users share information about new leaks and discuss best practices for password security. One Telegram post observed on [Date Redacted] stated, "Another oldie but goodie... lots of cleartext here, have fun."
Leaked Data Types
Ip · Address · Hash · Type · Email · Username · Passwords
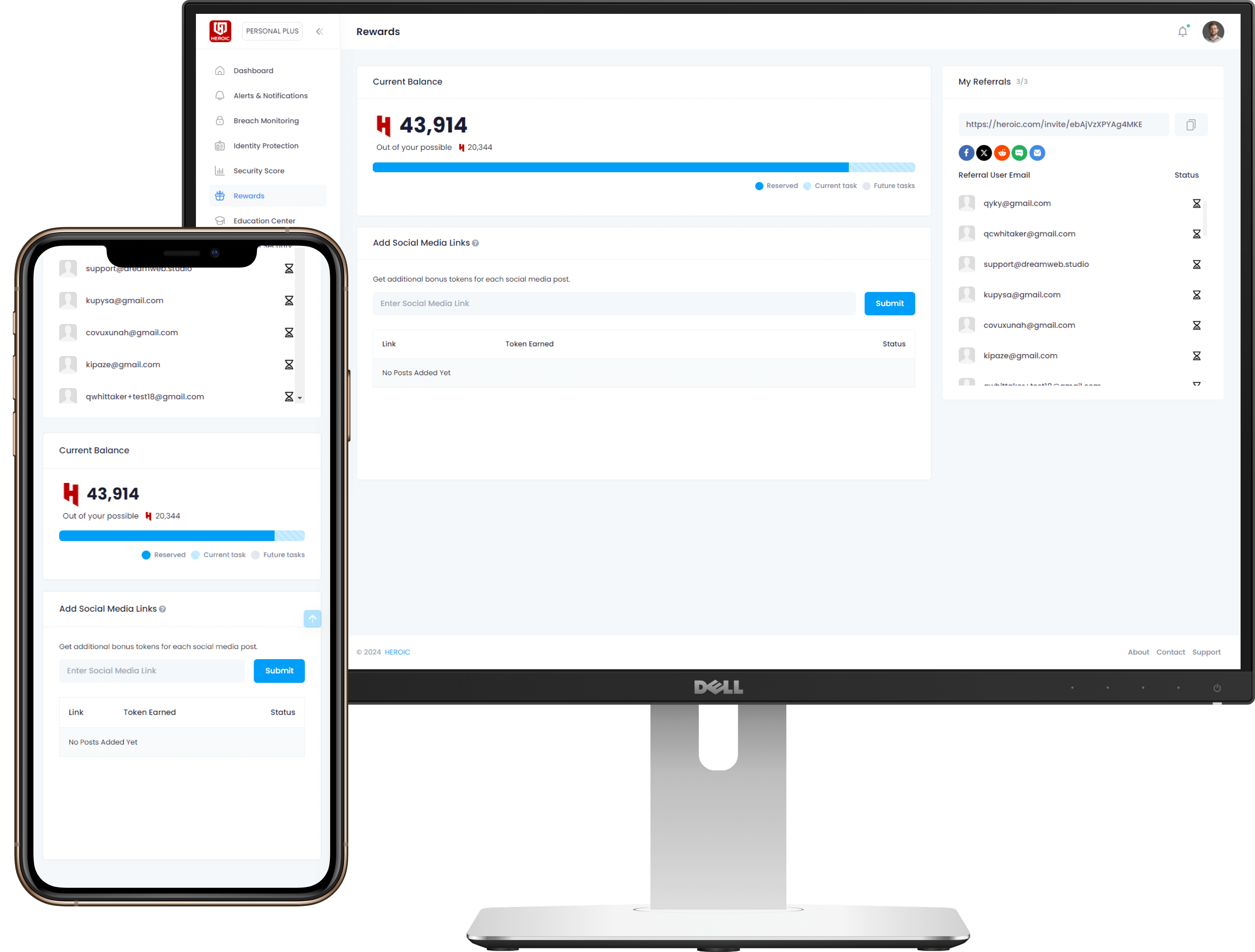
Get Early Access to the Guardian Platform
HEROIC is close to launching our next-generation platform where you can search, secure, and monitor all of your identities. To be the first in line, simply insert your email and you'll be added to the list

Be the first to know when we launch
Sign Up for Our Newsletter
Email marketing by Interspire



/qr-code.png)