
youximeng.com
Breach Details
Description
We've been tracking an uptick in older database dumps resurfacing on various hacking forums, often with cracked password hashes. What caught our attention with this particular dump was its age and the specific hashing algorithm used. While the volume of records, 25,390, isn't massive by today's standards, the reliance on MD5 with salt in September 2011 points to potentially vulnerable systems that may still be in use, or whose security practices haven't evolved sufficiently. The re-emergence of this data could provide attackers with a foothold into older, less protected accounts, especially if users have reused credentials across multiple platforms.
Youximeng.com: A Decade-Old Database Resurfaces
This breach involves a database dump from youximeng.com, an unspecified website, dating back to September 2011. The dump contains 25,390 records. It was discovered circulating on a popular hacking forum on October 26, 2024, after being indexed by our systems. The key detail here is the password hashing algorithm: MD5 with salt. While salting adds a layer of complexity, MD5 is considered cryptographically broken and susceptible to rainbow table attacks and collision attacks. This means that even with the salt, cracking these passwords is significantly easier than with modern hashing algorithms like bcrypt or Argon2.
The breach matters to enterprises now because it highlights the long tail of security debt. Organizations often struggle to decommission older systems or update legacy codebases. If youximeng.com represents a third-party vendor or partner from that era, the exposed credentials could potentially be reused to gain access to enterprise systems. Furthermore, the existence of this dump underscores the importance of regularly monitoring threat intelligence feeds for leaked credentials associated with your organization's domains and subdomains.
Key point: Total records exposed: 25,390
Key point: Types of data included: Usernames, passwords (MD5 with salt)
Key point: Sensitive content types: Potentially PII depending on the website's function
Key point: Source structure: Database dump
Key point: Leak location(s): Hacking forum (specific URL available upon request)
Key point: Date of first appearance: October 26, 2024
External Context & Supporting Evidence
While youximeng.com itself may not be widely known, the prevalence of MD5 hashing in older breaches is well-documented. Security researchers have long cautioned against its use. For example, a 2013 blog post by Troy Hunt detailed the continued risk posed by MD5-hashed passwords, even when salted. The re-emergence of these older dumps aligns with a broader trend of attackers targeting legacy systems and exploiting known vulnerabilities. This is often seen in attacks against small to medium-sized businesses (SMBs) that may lack the resources to maintain robust security postures. The fact that these credentials are still being circulated and potentially used demonstrates the continued value attackers place on even outdated data.
Leaked Data Types
None
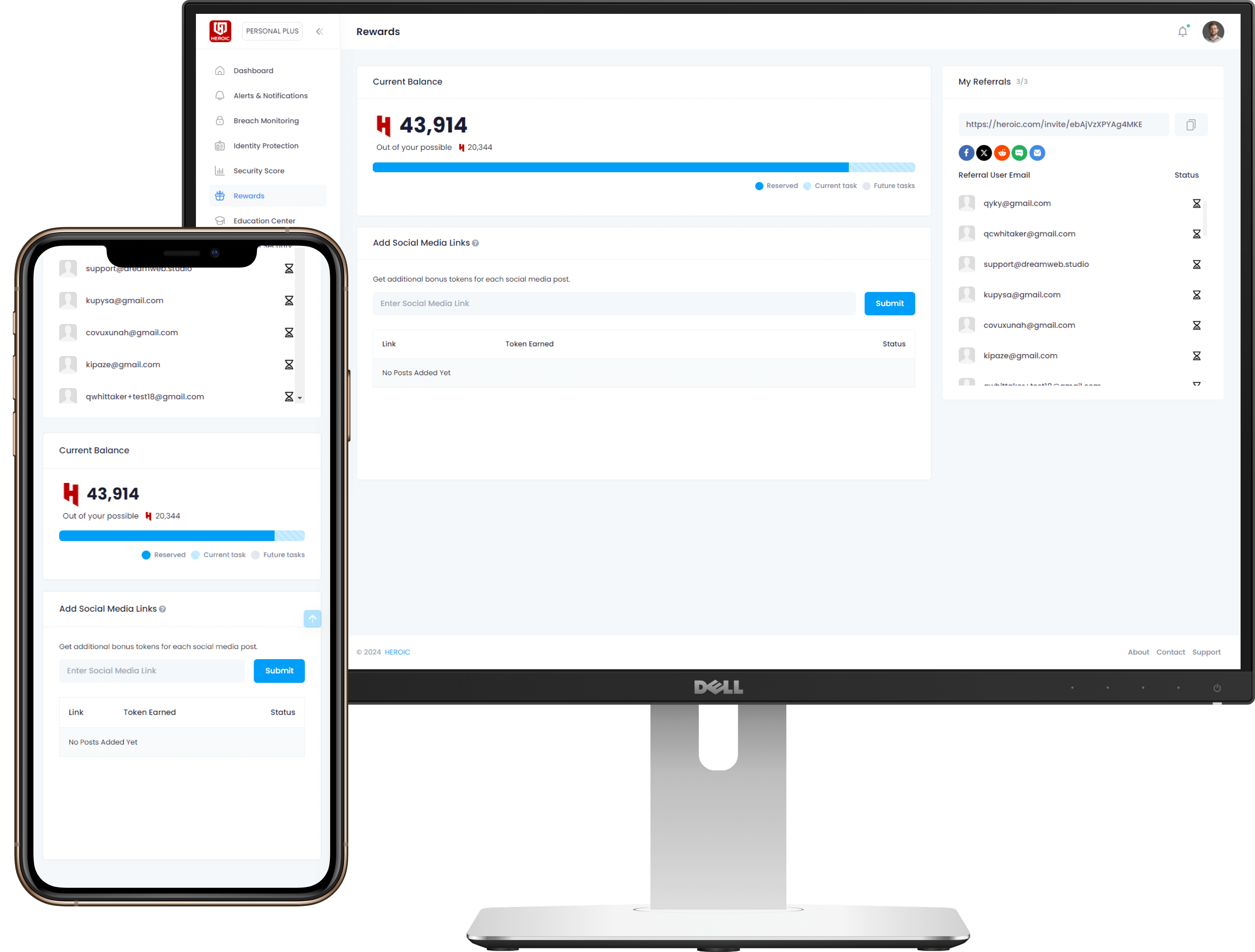
Get Early Access to the Guardian Platform
HEROIC is close to launching our next-generation platform where you can search, secure, and monitor all of your identities. To be the first in line, simply insert your email and you'll be added to the list

Be the first to know when we launch
Sign Up for Our Newsletter
Email marketing by Interspire



/qr-code.png)